Use cases to realize effective C-UAS solution (Most effective use cases)
Use cases of C-UAS protecting defense facilities and airports
While the utilization of drones continues to advance, the risks posed by suspicious drones are becoming increasingly serious each year. To address these risks, flexible C-UAS systems tailored to the specific challenges of each facility are required.
So far, we've explored the mechanisms behind C-UAS systems and how to choose the optimal system for each case.
Now, let's take a look at some specific examples of operational scenarios at several facilities.
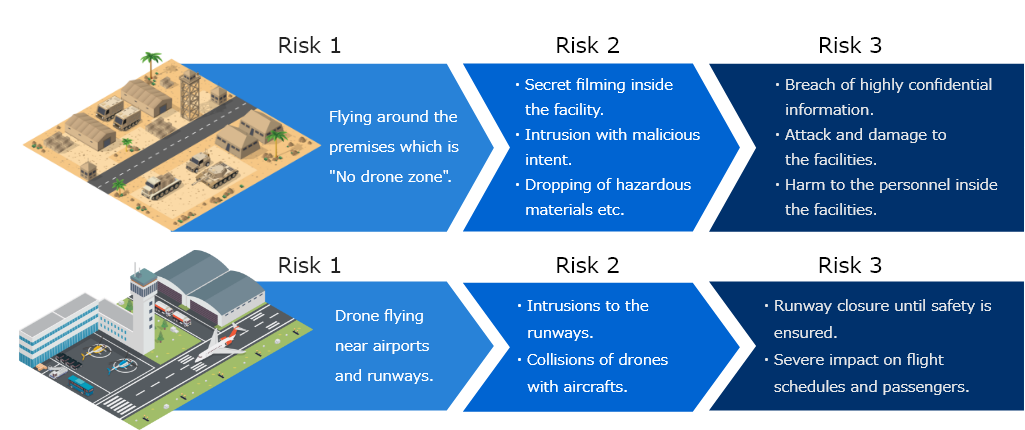
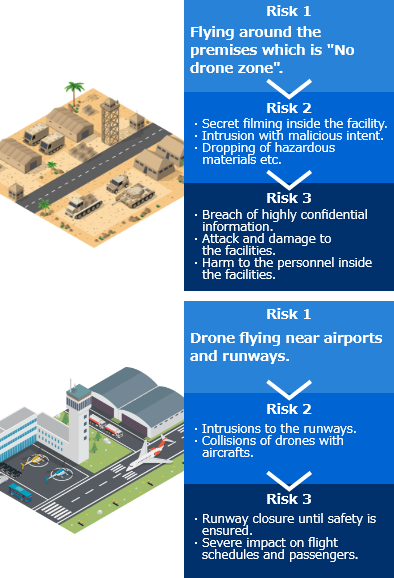
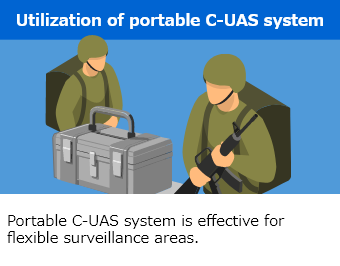
There are many critical infrastructure facilities, but the risks posed by intrusions of drones and the countermeasures required can vary depending on the facility.
That's right. So this time, let's take a look at operational case studies by focusing on defense facilities and airports, where countermeasures against intrusions of dangerous drones are essential.
Risks from intrusions of drones anticipated at defense facilities and airports
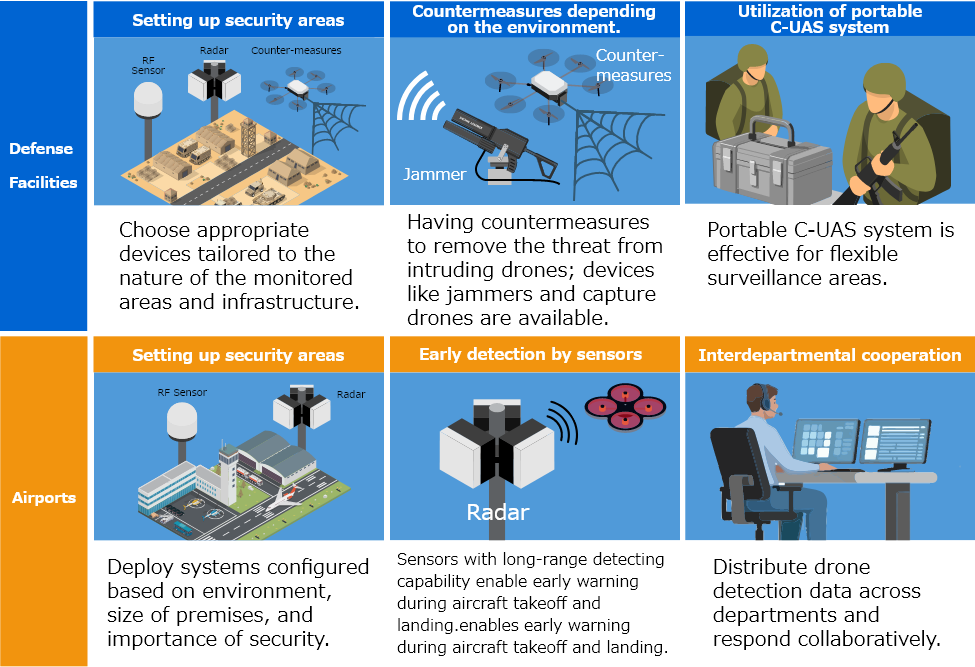
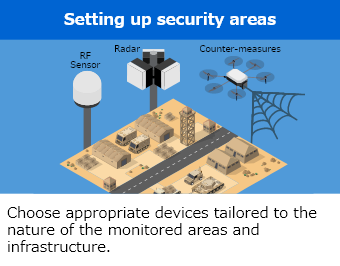
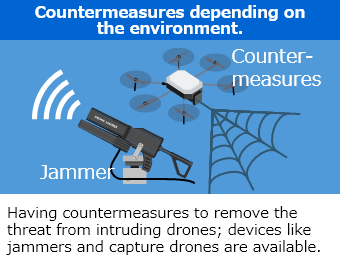
Examples of C-UAS applications
Importance of system configuration design to anticipated risks.
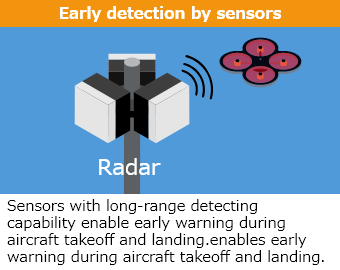
In addition to the countermeasures introduced here, it is effective to select equipment based on the risks that needs to be mitigated for each facility—for example, using radars with long range capability to detect reconnaissance drones approaching from afar, and deploying short- to mid-range radar and/or cameras to prepare for sudden intrusions by attacking drones.
While it is important for defense facilities to have mitigation options for dangerous drones, airports tend to deploy equipment specialized in detecting suspicious drones—highlighting the differences when compared.
That's right. While this comparison focused on defense facilities and airports, it's said that many other types of facilities will increasingly pay attention to and prepare for intruding drones in the future.
Recently, news which is related to drone intrusions has become more frequent. As drones become more familiar, more people are feeling the need to prepare for the risks of incidents caused by dangerous drones.
Risks expected at critical infrastructure facilities
As the awareness for security risk arising out of use of drones increases, the range of facilities requiring security against malicious drone intrusions is expanding. What types of facilities are considered to need countermeasures against such risks from drones?
C-UAS systems have already been implemented at major infrastructure facilities such as airports and defense facilities. However, I have heard that in recent years, even facilities that previously did not recognize the threat of suspicious drones are now seeing a growing need for such measures.
Exactly. While the use of drones is expanding, cases of misuse—such as intrusion and illegal filming—are also increasing.
That’s why even facilities closely connected to our daily lives, like data centers and plants, are now getting aware of the needs to introduce C-UAS solutions. Let’s take a look at the risks expected at such facilities.
Expected Risks from Drone Intrusions
Intrusion by just a drone can lead to serious
affect to infrastructure and our everyday life.
Any facility can be threatened by intrusions of malicious drones.
Preparation to such risks is essential and required.
Now that the awareness to drone threats to the infrastructure facilities are growing drastically. Incorporating regular aerial threat awareness into your security can lead to effective defense in critical situations.
Now that I can see the risks of drone intrusion to each facility can lead to quite serious social problems.
To avoid confusion in an emergency, it is important to know the risks and countermeasures in advance. By having this knowledge, you can feel secure and avoid unnecessary fear.
That’s right. And it's a good thing that the awareness and interest to security against such threat is growing throughout the security personnel in the world.
The Relationship Between Next-Generation UAS
Traffic Management Infrastructure and C-UAS
As the use of drones continues to expand, efforts are underway to establish regulations and implement preventive measures to avoid accidents. Among these initiatives, one of the most important infrastructures gaining attention is the UAS Traffic Management (UTM) system. But what exactly is UTM?
I heard that with the 2022 amendment to the Civil Aeronautics Act, drones can now be flown beyond the operator’s visual line of sight in Japan as long as the required pre‑applications and conditions are met. The possibilities for drone applications just keep expanding!
That’s true! But as more drones operate in the airspace — including those flying beyond visual line of sight — the risk of accidents such as mid‑air collisions is also said to be increasing. To prevent these incidents and ensure safe drone operations, the importance of proper operational management, essentially an air‑traffic‑control function for drones, has been growing.
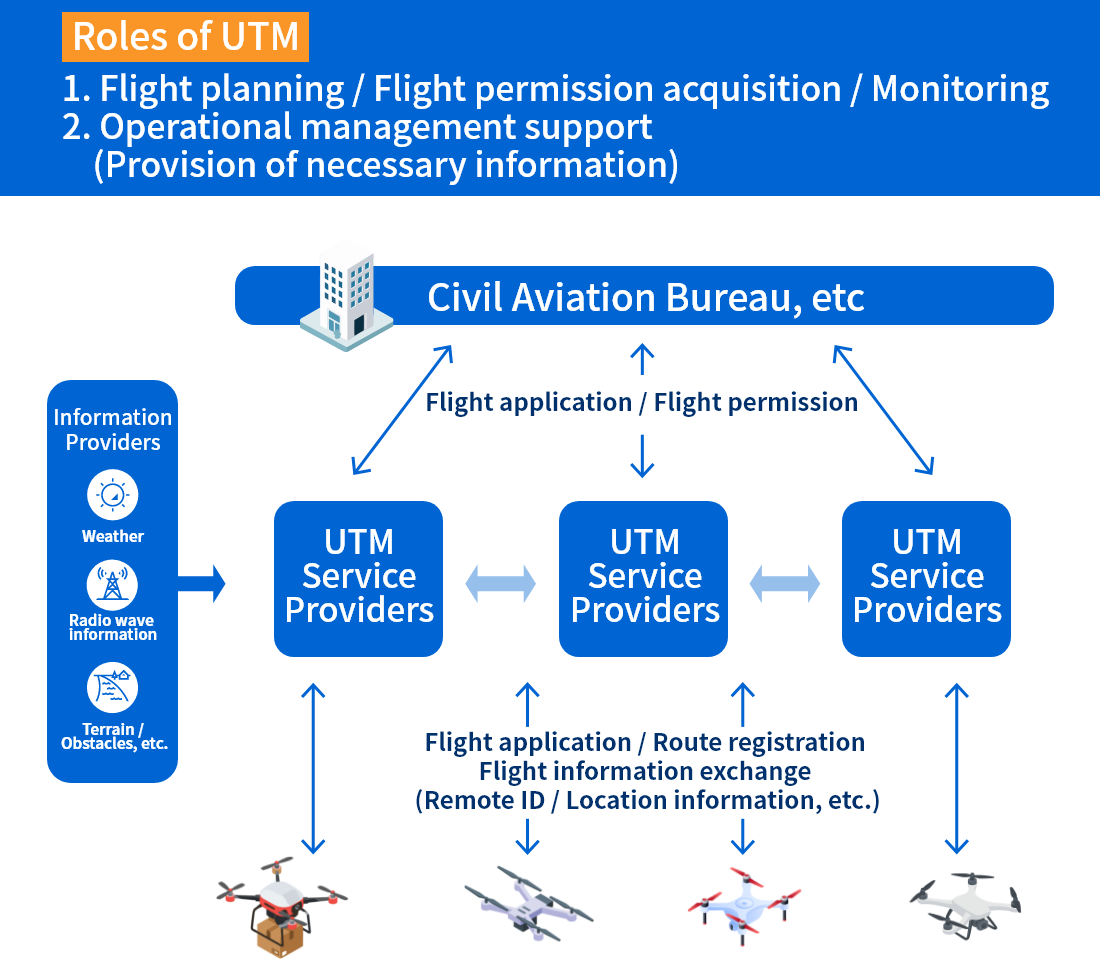
I see. And that’s why the development of Unmanned Traffic Management, or UTM, is now moving forward toward practical implementation. What kind of system is UTM exactly?
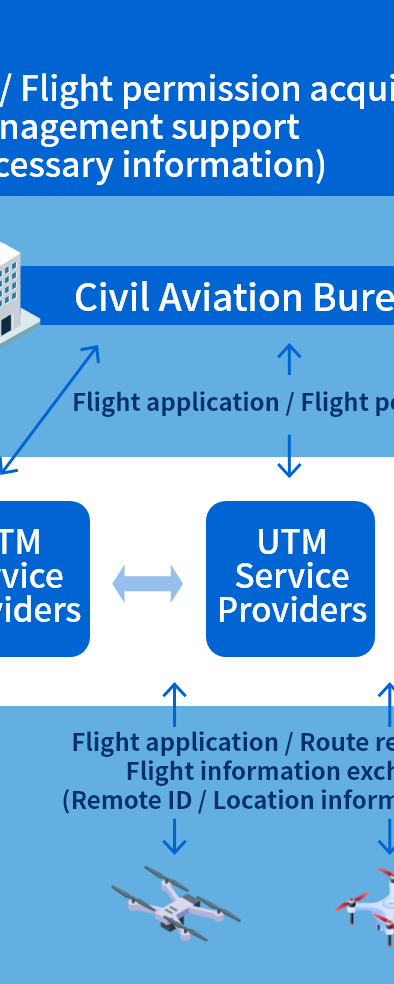
What Is UAS Traffic Management (UTM)?
I understand. So UTM supports safe flight operations by monitoring the real‑time flight information of multiple drones and communicating alerts, such as potential hazards. But if there are drones that haven’t submitted their flight information or don’t carry Remote ID, wouldn’t it become difficult to accurately monitor the airspace in real time?
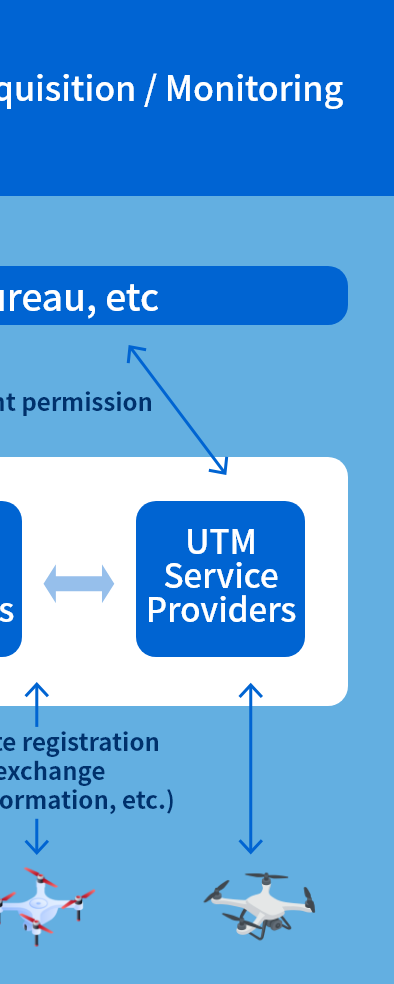
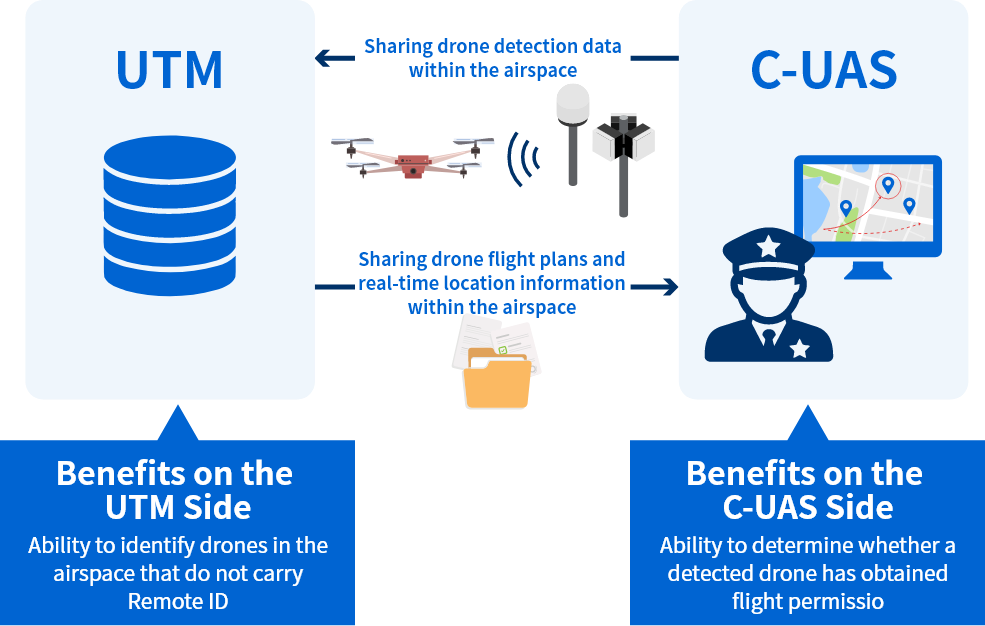
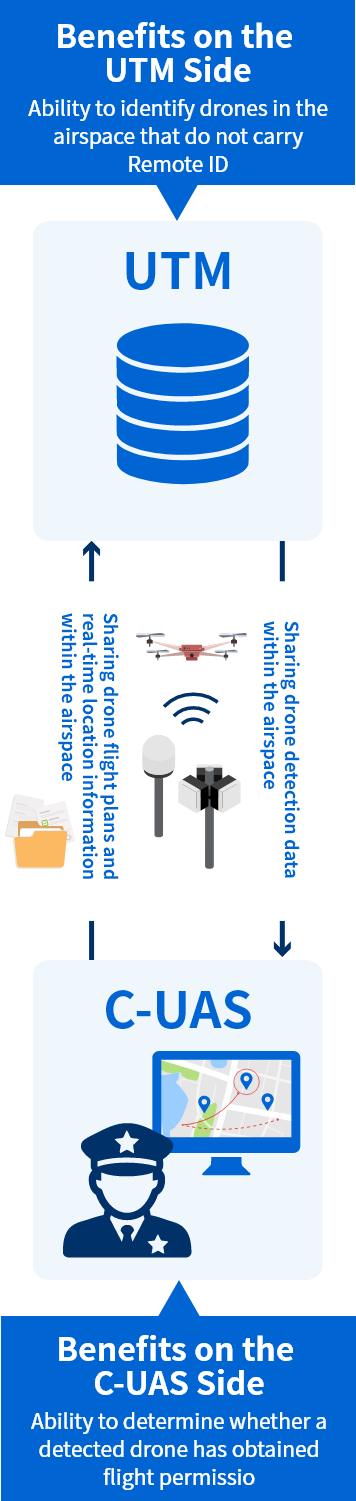
That’s an excellent point! You’re right — drones without Remote ID cannot be detected by the UTM. That’s why integrating UTM with a C-UAS can be very effective. By sharing data between the two and complementing each other’s information, it becomes possible to improve the reliability of airspace monitoring.
Example of UTM and C-UAS Integration
Unlocking Synergy Through the Integration of UTM and C-UAS
UTM, which manages air‑traffic control for drones, and C-UAS, which detect and respond to suspicious incoming drones, are both essential infrastructures for building a safe drone‑enabled society. By integrating data between the two, we can further enhance safety in the utilization of drones.
Throughout this fourth installment, we’ve explored both the evolution and the challenges of a drone‑enabled society. It seems clear that both C-UAS and UTM will play major roles in promoting the proper and responsible use of drones.
Exactly! To build a society where everyone can enjoy the benefits of drones with peace of mind, both systems will surely become indispensable.
Yes, absolutely. Let’s continue to watch together as the world of drones keeps expanding!
C-UAS Solution
Toshiba offers a comprehensive system that detects, tracks, identifies, and mitigates threats from suspicious drones.