IoT Security Solution CYTHEMIS™
CYTHEMIS™ secures and visualizes infrastructure control systems and industrial production systems in one single control platform. Also legacy equipment without built-in security mechanisms is protected.
CYTHEMIS™: end-to-end security solution
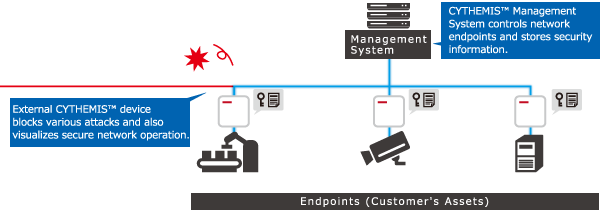
CYTHEMIS™ is an end-to-end security solution to protect critical infrastructure control systems and industrial production systems which use IoT (Internet of Things). It comes as a package solution consisting of external hardware protection devices and management software. These hardware boxes provide endpoint security on any OS and equipment including legacy versions and even discontinued platforms.
POINT1
Secure Network
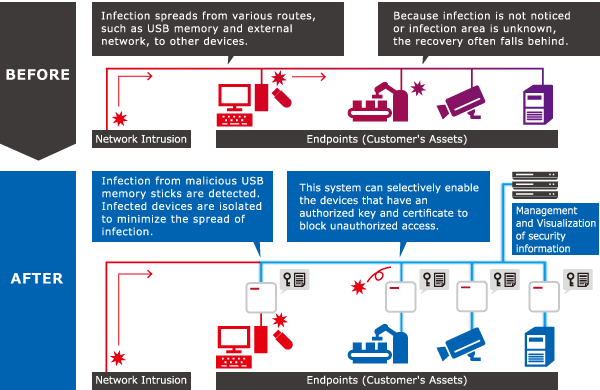
Unauthorized access and malware infections are blocked by using device authentication between endpoints. The network architecture is visualized in CYTHEMIS™ control software.
POINT2
Prevention of USB Infection Spread
Malware infections which may occur during maintenance work via USB memory are detected and their spreading within the network is prevented.
POINT3
Easy Installation
Easy Installation with external devices on any OS and legacy equipment.
Please check the product overview video

*Links to YouTube.
Hardware Based Secure Protection
Network attack occur through various intrusion routes such as external networks, a USB memory and others. With its external hardware devices CYTHEMIS™ blocks most of such attacks: communication to and from any network resource can happen only between those ones connected to a CYTHEMIS™ hardware device with the right keys and certificates. The CYTHEMIS™ Management System manages network access through strict rules and policies.
Security and safety in various scenes.
CYTHEMIS™ establishes a secure environment in a wide range of scenarios including infrastructure facilities and factories where security measures are otherwise difficult to implement. Where applicable, remote maintenance can be also realized by CYTHEMIS™.

Infrastructure facilities and factories for which security measures are difficult to implement due to the mixture of legacy equipment

Equipment that handles security related data such as surveillance cameras and POS (point of sale)

Equipment that requires remote maintenance
Product Specifications - Form of Delivery
| Supported Protocol | Protocol operating over TCP and UCP |
|---|---|
| Interface | RJ-45 |
| Power | AC or USB Power |
| Management System | On-premises or Cloud* |
| Security Certification | CC (ISO/IEC 15408)* |
| Device Size | L: 84mm x W: 84mm x H: 38mm |
| Device Mass | Approximately 170g |
| Product Series | Wifi, POE* (power over ethernet) |
- * These features are planned for further versions
Contact us
Please read the notes before contacting us.
MAIL. TISS-cythemis@ml.toshiba.co.jp
By sending your personal data, you shall be deemed to consent to the following.
- We use your personal data for the purpose of answer and dissemination from our company or group companies.
- Our group companies or third party contractors may use your personal data to the extent necessary to respond to your inquiry.
- You can request us at any time to disclose, correct or delete any personal data on you that we have retained. Please contact the division indicated above.
- You can choose not to disclose your personal data, but doing so may prevent us from responding to your inquiry.
- Please see Privacy Policy.
- Children under 16 years old are requested to make an inquiry only after receiving the consent of a parent or guardian.
- Inquiries sent on Saturdays, Sundays, or during company holidays, will be received on the earliest working day and dealt with as soon as possible.



