- Vol.
- 34



Cyber physical systems (CPS) contribute to the development of industry and the solving of social issues by collecting and storing data produced by people and objects every day in the physical (real) world and analyzing it in the cyber (virtual) world to create new value. CPS will soon become a common part of daily life. It will be the era of Data 2.0, when value is created from data. In the era of Data 2.0, data security measures will be more important than ever. Toshiba has established a specialized organization to research and develop advanced security technologies. This article explains the data security technologies that promote the distribution of data and utilize it securely.
-
What technologies are used to securely manage and utilize data?

-
Secure data processing technologies for distributing industrial data

-
Provided information control technologies, giving data providers with peace of mind

-
Contributing to business with safe security technologies that are essential for leveraging data

 What technologies are used to securely manage and utilize data?
What technologies are used to securely manage and utilize data?
Toshiba has created a new research and development organization called the “Cyber-security Technology Center.” In order to provide continuous protection against security threats not only for the field of information systems, but also for the control systems used to optimally operate social infrastructure and industrial equipment, this organization researches and develops advanced security technologies.
Toshiba aims to realize safe, secure, and prosperous societies, and it is working hard to leverage the various data generated by CPS and supply it to customers to help them solve their problems and create new value. In the era of Data 2.0, in which this data will be a source of value, there will be a greater need to distribute data to external parties, so that the data accrued in-house can be subjected to sophisticated analysis and converted into new value, or supplied as value itself, instead of merely shutting it away in-house. To do this, it is vital to have a data service platform capable of working with large amounts of accumulated data. Let’s look at two of the security technologies required for this data service platform that Toshiba has its attention focused on: “Secure data processing technologies”, which are used to protect confidential corporate information, and “Provided information control technologies”, which protect the personal information provided by data providers.
 Secure data processing technologies for distributing industrial data
Secure data processing technologies for distributing industrial data
First, let’s look processing technologies for securely providing industrial data to outside parties. This industrial data consists of data gathered by companies from products and services, and is of great importance to companies. Company industrial data is already being used to improve productivity through internal analysis and worksite feedback within individual companies. However, when companies have difficulty developing methods for analyzing data in-house, they contract out their development to outside parties such as analysis companies, and supply the industrial data to these contractors.
The Toshiba Group, for example, leverages industrial data in its semiconductor production processes. In this example, AI, pattern mining, and other technologies are used to reproduce the experience and expertise of veteran engineers in the semiconductor production field. We have developed unique analysis methodologies for using processing history data for semiconductor products and wafer maps (which indicate the positions of non-defective and defective chips on wafers) to forecast which production equipment is responsible for product defects. This was made possible by collaboration between semiconductor engineers and AI engineers, and has produced major results, such as production efficiency improvements.
Developing these analysis methodologies requires wafer processing history data and wafer maps, both forms of industrial data. However, processing history data can be used to infer the names of the production equipment that performed processing, the order in which processing was performed, and processing times. Likewise, wafer maps can be used to calculate production volume and yield (the percentage of usable products). Supplying this information to an outside analysis company runs the risk of the leakage of corporate secrets such as technical levels, production plans, and manufacturing costs, as well the copying of production lines.
That's why we turned our attention to secure data processing technology, used to safely and securely provide industrial data to outside parties.(Fig.1)
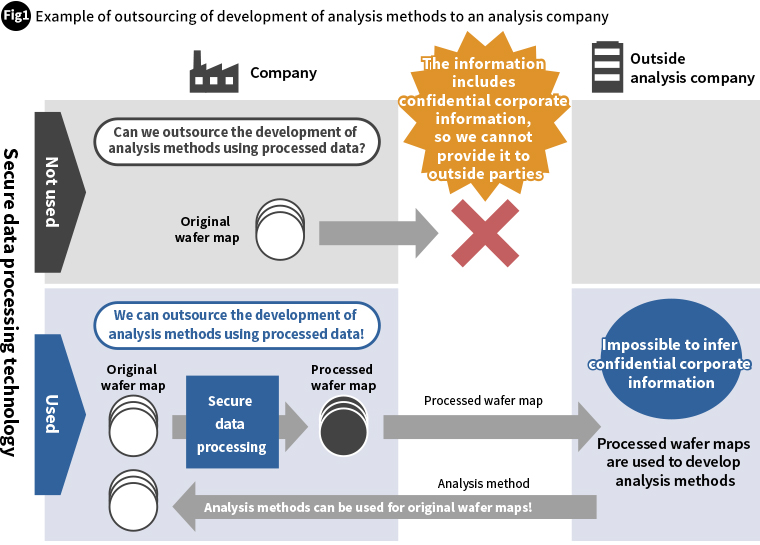
The key is to remove all information that could be used to infer confidential corporate information (ensuring security) while leaving sufficient valuable information to be used in the development of analysis techniques (ensuring usability). We have tried various approaches for achieving a balance of security and usability, researching and developing diverse data processing technologies. Allow us to introduce some of these technologies for directly processing original industrial data to protect data.
This technology deletes wafer maps at constant spaces. The spaced deletion changes both usability and security. We confirmed what spaces would be sufficient to provide the same level of accuracy when analyzing the causes of product defects as using the original wafer map (ensuring usability). We also confirmed what spaces would ensure a sufficient level of security with regard to yield estimates (Fig.2).
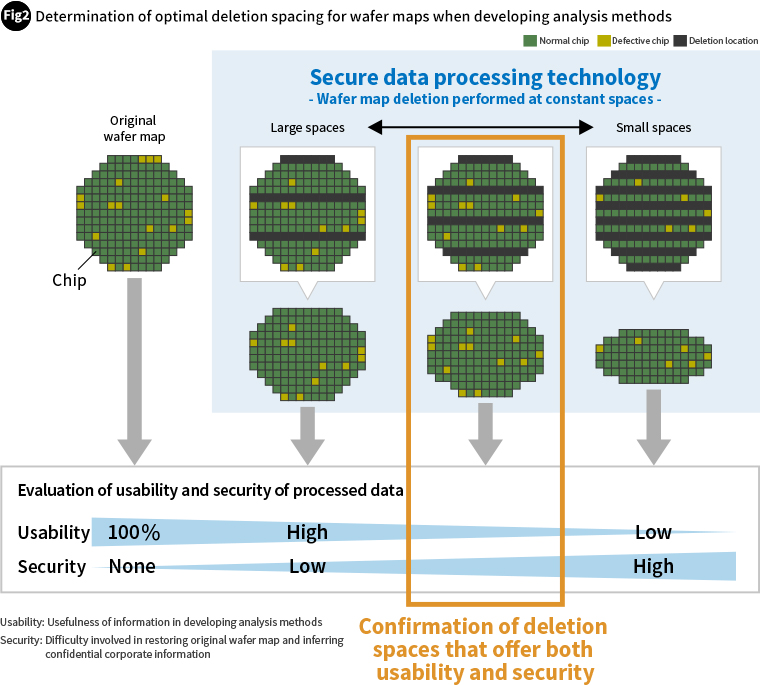
We have promoted the use of this technology in the security industry through academic conference presentations in Japan and the like while carefully deliberating the validity of the methods used to evaluate its security, a critical consideration for customers.
By establishing this technology, we hope to contribute to the distribution and leveraging of data throughout the world by enabling companies to feel secure in providing their industrial data to outside parties, helping further improve their own productivity, creating new business that converts data into value, and creating greater social value.
 Provided information control technologies, giving data providers with peace of mind
Provided information control technologies, giving data providers with peace of mind
Carrying out sophisticated security design in advance is important for flexibly providing services in compliance with laws and regulations while building data service platforms for securely managing and leveraging data.
To provide data providers with peace of mind, we employ various techniques during the security design stage. These include methods of checking when provided data is used, where it is used, and how it is used, as well as methods of processing data so that even in the event of a data leakage, it would not possible to determine providers or personal information from the leaked data.
Let’s look at some specific examples. One of business areas that the Toshiba Group is developing is precision medicine. In this business area, we are developing data service platforms for securely storing, analyzing, and leveraging peoples’ genome data, medical examination data, and medical expense statement data. By storing many people’s genome, lifestyle, and other data, we hope to assist in the recovery not only of individuals but of other people with the same symptoms or fears of the same illnesses, and to contribute to the next generation of preventative medicine.
For example, genome data for tens of thousands of people is necessary for predicting the risk of lifestyle-related diseases. The first data used for this project was provided by Toshiba Group employees with whom the project’s aims resonated and who agreed to supply their own personal information. The genome, medical examination, medical expense statement, and other data that was used was the personal information of employees, and needed to be handled with the utmost care. It was therefore critical that we create a system which would put data providers at ease and enable them to provide their data with peace of mind.
Toshiba has already implemented measures to address the concerns of data providers by pseudonymizing and encrypting individual data before storing it to prevent the worst case scenario of individuals being identified from the data in the event of a data leakage. To provide even greater peace of mind when providing data, we focused on data utilization consent information from data providers. Even if a provider consents to the use of data, in accordance with the law, consent must be received again before using the data in new ways. That’s why we needed to create a system that could get consent from data providers without placing a burden on them, and which would allow them to see how their data was being utilized after they provided consent. To achieve this, we used provided information control technologies, which are based on blockchain technology, to provide a system capable of highly transparent consent history and usage history management.

 Contributing to business with safe security technologies that are essential for leveraging data
Contributing to business with safe security technologies that are essential for leveraging data
The Toshiba Group is working to commercially release its data services, and to do so it is building data service platforms that handle diverse data such as manufacturing, O&M, purchasing, and personnel data. While the nature of this data varies, in order to increase the number of service users (data providers), it is vital, no matter which data, that we implement security measures that enable data providers to provide data with peace of mind.
The quest for greater security is an unending one. We in the Cyber・security Technology Center will continue to design and develop even more robust security so that the Toshiba Group can serve as a leader in the Data 2.0 era. We will use our advanced technologies and skills to contribute to the businesses of all of our customers.
- ※
- The corporate names, organization names, job titles and other names and titles appearing in this article are those as of August 2020.