Protecting the Internet of Things (IoT) from the growing threat of cyber-attacks requires system characteristics to match security requirements, as well as ongoing measures in which cost and technology are balanced. Based on the concept of Security Lifetime Protection, Toshiba Digital Solutions has developed Security Reference Architecture, a systematic framework for building up security in a flexible, robust manner which is matched to the breadth and depth of IoT systems from the design stage. We are organizing which measures are to be implemented and carrying out verification testing so that we can provide this framework to customers in the future. Let's look at this Security Reference Architecture in depth, and explore the key points of solutions based on it.
Enhancing security by design
The IoT connects all types of objects to networks. This means that even control systems, which have so far been managed in closed environments, are becoming open. The IT (information technology) and the OT (operational technology) including control systems must be comprehensively protected. What kind of security, appropriate for the IoT era, can provide end-to-end protection, covering everything from edge devices such as sensors and other equipment to networks and applications? Conventional security solutions focus on individual attack points, but the cyber-attacks which target vulnerabilities in devices and networks are constantly evolving, and it is clear that this approach will no longer be sufficient enough.
In order to meet this constantly changing threat, Toshiba Digital Solutions believes that IoT system security must take a proactive approach. It is too late to respond to a security threat after it has occurred. A posture must be taken which optimizes security before new threats are encountered.
Based on this concept, we formulated the new Toshiba industrial IoT security concept, "Security Lifetime Protection." It uses a PDCA cycle of design and defense; operation monitoring, prediction, and detection; incident response and recovery; and evaluation and verification to handle security, which otherwise comparatively degrades as cyber-attacks become more advanced and sophisticated. The goal is to ensure sustainable security that protects entire IoT systems.
* The formulation of the Security Lifetime Protection and a diagram of the
PDCA cycle are introduced in-depth in #01.
* PDCA: Plan - Do - Check -
Action
Of particular importance are the assessment and design phases, which aim to achieve security by design. Based on the PDCA cycle, they implement security in consideration of lessening vulnerability and countermeasures against the threats from the system planning and designing phase. When systems are released, not only do they provide security against known threats, but also security based on the results of past risk assessments and vulnerability verification.
Click here to move to the top of this page.
Developing measures based on the evolution and importance of the systems to be protected
However, appropriately designing IoT system security is no easy matter. Elements such as the businesses and services to be protected, operation processes, types and numbers of connected devices, handled information assets, and security risks that can result in security incidents vary from one IoT system to another.
Using the same methods to deal with everything from state-sponsored attackers to small criminal organizations and amateurs is not a reasonable approach. Excessive security measures can reduce the efficiency of operations and systems, while insufficient measures can cause ballooning costs due to the need for additional follow-up security measures. This could lead to Security Lifetime Protection itself failing to function.

This is why we prepared a systematic framework that aligns diverse IoT system security-related technology elements with the properties and advances of systems. This is our Security Reference Architecture* industrial IoT security framework.
* Security Reference Architecture is introduced in detail in #01.
Based on the evolution of digital transformation, three security measure levels ("Low," "Middle," and "High") are defined based on the IEC62443 international standard, and technical measures that satisfy the requirements of each level are decided on and implemented in individual systems. The PDCA cycle is continuously applied to Security Lifetime Protection, with this architecture as its platform. This makes it possible to continuously design sufficient security based on advances in individual systems, as well as their importance, while balancing costs.
Click here to move to the top of this page.
Defense in depth based on the breadth and depth of IoT systems
In designing the Security Reference Architecture, we have systematized necessary measures based on the axes of IoT system breadth and depth. This is our "dual axis defense in depth" (Fig. 1).
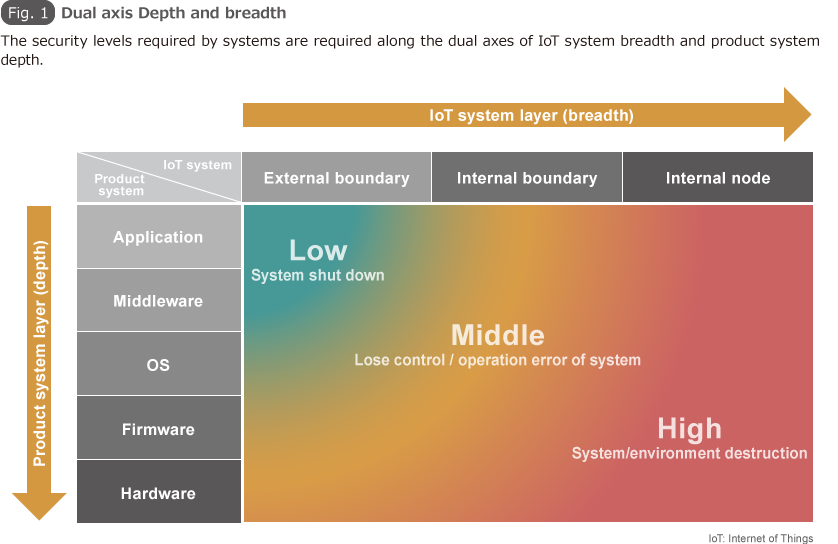
Breadth is used to clearly indicate the range of measures required as IoT systems evolve. During the visualization stage, it focuses on risk management along external borders in order to prevent systems from being shut down. During the optimization stage, it expands the scope of measures from control systems to external contact points (internal borders) to prevent erroneous operation and keep systems from running out of control. During the automation and autonomy stages, layers of protection are applied even within internal control system nodes to prevent major incidents which could have serious impacts on peoples' lives or the environment.
The depth axis, on the other hand, is used to organize which measures to apply to which of the five system layer: the application layer, the middleware layer, the OS layer, the firmware layer, and the hardware layer. Threats to the application layer are combatted using malware countermeasures such as whitelists and basic measures such as firewalls and other security software. For threats to the middleware, OS, and firmware layers, hardware measures are used, such as secure booting, which ensures the integrity of firmware, boot code, OS kernels, device drivers, and the like by sequentially verifying them based on their startup sequence. For threats to the hardware layer, and the system as a whole, sophisticated and advanced attacks which seek to stop security functions are handled through measures such as limiting access from ordinary applications by using virtualization technologies to separate security functions and manage them independently.
Click here to move to the top of this page.
Three security models and an innovative solution that implements them
In implementing dual axis defense in depth, we handle the breadth of IoT systems by focusing on technology development. We have established a three security model. The Out-Of-Bound (OOB) model applies to the physical boundaries between systems and external elements, and contact points with external networks. The TOUCH model securely manages the boundaries between individual subsystems within systems. The INLINE model includes measures for internal nodes such as individual devices and pieces of equipment. We are organizing which measures are used by each model, and carrying out internal verification testing (Fig. 2).
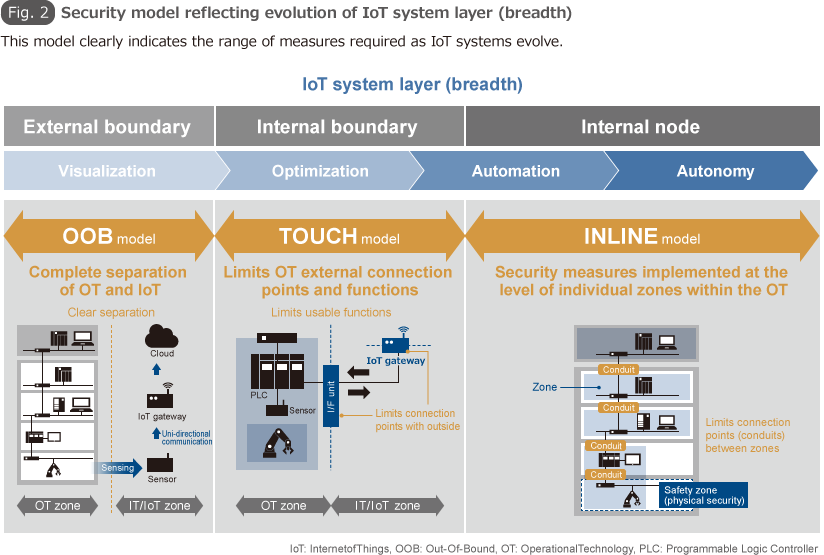
The OOB model uses zoning, the complete separation of the IoT from the OT zone, and focuses on ensuring data integrity. It uses data diodes when transmitting data regarding sensing field devices. These data diodes physically limit the flow of data in a single direction, from control systems to information systems. This has no impact on the control system process.
For the OT zone, the TOUCH model narrows down the number of devices that can be connected to externally to only those for which external connection is essential, with the aim of preventing incidents from affecting the critical functions of control systems. Executable programs are limited in advance using whitelists, and the number of commands that can be remotely used to control devices is restricted. This produces an environment which is capable of on-demand acquisition from field devices only of the data necessary for analysis and optimization.
The INLINE model uses function-level zoning and restricts the contact points between zones, ensuring a high level of security for the entire control system. Artificial intelligence-based next-generation malware countermeasures* are used in the zones closest to information systems. Data diodes, uni-directional security gateways, are used on the contact points between information system zones and control system zones. Whitelist-based malware countermeasures* are used on embedded devices within control system zones, and products with Embedded Device Security Assurance (EDSA) international certification are used as industrial controller products. Furthermore, our solution detects abnormal behavior by OT networks and components, uses monitoring solutions, optimally combines measures for each zone, and implements high-level measures that meet critical infrastructure security requirements.
* AI-based next-generation malware is introduced in detail in #03.
* Whitelist-based malware countermeasures are introduced in detail in #05.
Toshiba is also developing secure proxy devices, applying the security technologies it has developed through its IC card business. These devices provide secure communications and mutual authentication between devices, without directly modifying endpoint devices themselves, by installing proxy devices between devices and upstream networks. They ensure data confidentiality and integrity without reducing availability. We are currently conducting internal verification of these devices as a revolutionary solution that increases overall system security without directly modifying legacy endpoints.
Based on Security Reference Architecture, Toshiba Digital Solutions is promoting Security Lifetime Protection while also working to create security solutions in line with the advances of digital transformation. We will flexibly update technical requirements, link diverse systems and approaches, and provide highly reliable IoT security to combat increasingly sophisticated and advanced security threats.
* The corporate names, organization names, job titles and other names and titles appearing in this article are those as of May 2018.