Digital transformation led by the Internet of Things (IoT) is beginning to grow in a wide range of industrial and societal fields. This new world, to which products, information systems, and control systems are becoming connected, is accelerating business model transformation, but it also comes with the risk of a wider range of channels for cyber-attacks and other threats. In fact, the number of attacks against the key infrastructure for people has increased on world-wide basis via slight vulnerabilities of devices connected to the network. Security threats are no longer problems for individual companies and plants alone, but have become major problems for society as a whole. To combat this threat, Toshiba has systematized its extensive experience in providing security operation management for both information and control systems. It is complying with international standards and strengthening its efforts, enhancing preparations and developing innovative technologies.
The light and shadow of digital transformation
The advance of digital transformation is poised to bring about major changes to industry and social infrastructures. The movement of products and people will be collected in the form of data from sensors and cameras and analyzed in detail in cyber (digital) space. It will be possible to feed the new value discovered through this process back into the real world with unprecedented speed.
On the other hand, the connection of diverse systems, massive numbers of facilities and devices, and countless users will also bring about new, heretofore unimagined threats. Among these, of particular concern are security risks for the control systems that support the vital infrastructure that supports peoples' lives, such as energy, manufacturing, transportation, and medical facility infrastructure. These systems, which in the past were operated independently, without being connected to networks, may become targets as they are connected to the IoT. A single sensor or camera with security vulnerabilities could be pinpointed and used to attack an entire system.
Looking at actual cyber-attack damage in recent years, it becomes evident that social infrastructure is being targeted at an accelerating rate. The massive power outage that occurred in the Ukraine in 2016, cutting off power to several million households, was caused by systems in the power company, located in the country's capital, being infected by an unknown form of malware. From 2016 to 2017 numerous vulnerabilities in medical devices became evident, and it had been pointed out that there was a potential danger that these devices could be taken over and remotely controlled, threatening peoples' lives. Ransomware*, which became rampant in 2017, affected operations in many plants and social infrastructure sites, causing major damage worldwide. Security threats, which were once an issue for information systems, are beginning to affect the area of control systems, which have an impact on peoples' lives and safety.
* Ransomware: This new form of malware has become widespread in recent years. It locks up infected computers or encrypts files, making them unusable, and then demands a ransom to return them to their former state.
The commodification of cyber-attacks is adding further fuel to these threats. As long as the tools for carrying out cyber-attacks are easily purchasable over the net, anyone can use cloud services to easily obtain an environment for carrying out attacks. There is no way to predict when or where attacks those threaten not only business continuity but also society and peoples' lives will occur, or who will carry them out.
Click here to move to the top of this page.
Measures that address both information systems and control systems
Toshiba's mission is to support customer business continuity during the IoT era of digital transformation, producing a safe, secure society. To achieve this, it is essential to identify the convenience offered by the IoT and the threats it presents, shifting from the past security measure approach that focused on defense to the one based on ensuring sustained security that encompasses both information systems and control systems.
The key point here is the difference in the security needs of these two types of systems. For example, of the three principles of security ? "confidentiality," "integrity," and "availability" ? for information systems, which focus primarily on protecting information resources such as customer information and confidential information, the highest priority is confidentiality. For control systems, on the other hand, for which risk management includes people, products, and services, the highest priority is to protect the safety and health of workers and neighborhood, and to maintain environmental levels while ensuring the continued operation of devices and systems ? that is, "availability."
Toshiba has a long history of social infrastructure development, and has proposed and implemented diverse security measures based on a deep understanding of customer worksites. We also have an extensive track record of supporting the operation of IT infrastructure used by roughly 200,000 Toshiba Group employees around the world. We securely manage a vast number of information devices, protecting the security of all parts of global networks as we continue to accumulate extensive knowledge regarding responding to cyber-attacks.
Toshiba has systematized expertise regarding its security operation. We have now begun an innovative measure to provide customers with resilient and sustained IoT security. This initiative is the formulation of a new Toshiba industrial IoT security concept, "Security Lifetime Protection." We have also established a Cyber-Security Center that aggregates our Group's security functions. Furthermore, we are conducting further development of security solutions that encompass both information systems and control systems.
Click here to move to the top of this page.
The "Security Lifetime Protection" IoT security concept
Information system security management (ISMS) of which guideline is stipulated by ISO*/IEC* requires organizations to implement periodical PDCA cycle that entails situation assessment, prevention, detection and countermeasures. These systems have certification systems which require that organizations continuously implement the PDCA* cycle of situation assessment, prevention, detection, and countermeasures.
* ISO: International Organization for Standardization,IEC: International Electrotechnical Commission,PDCA: Plan-Do-Check-Action
Based on this concept, Toshiba has formulated unique "Security Lifetime Protection" for use in industrial IoT systems, IoT systems in industrial fields which include control systems used in industry and social infrastructure (Fig. 1).
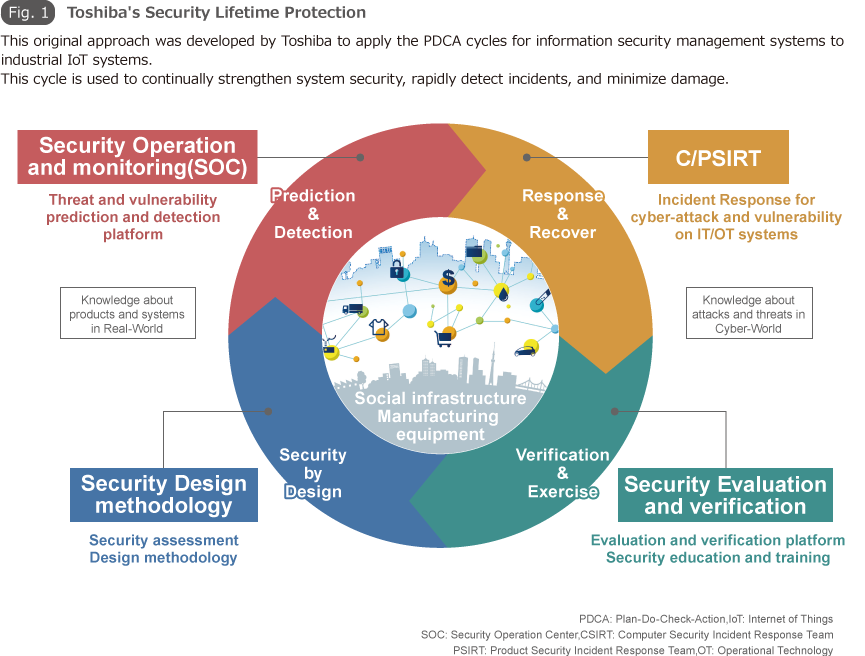
By implementing a relentless PDCA cycle of design and defense, operation monitoring, prediction, and detection; incident response and recovery; and evaluation and verification to handle security, security measures which have been degraded by advanced attacks are able to be kept up to date. The goal is to ensure sustained security that takes "health, safety, and the environment" into consideration in addition to the three core principles of security, "confidentiality, integrity, and availability."
Toshiba has developed a system that ensures security quality in every phase through product development in compliance with IEC62443, an international security standard for control systems, and that provides a platform for monitoring vulnerabilities and incidents based on product configuration management. Furthermore, Toshiba works to strengthen security by strictly stipulating incident response rules, priorities, risk management policies, and the like in internal regulations, enabling it to improve recovery efficiency in the event of security issues. It also maintains an environment for constantly performing the latest security evaluations and verification and enhances security by developing security personnel through training and hands-on exercises. In the design and defense phase, in particular, Toshiba has developed a unique design methodology based on the concept of "security by design" starting from product and system design stages, and has stipulated that component and product selection and risk management be conducted in a rigorous manner. Building in a degree of security quality from the initial development stages helps make later PDCA measures more effective.
This Security Lifetime Protection is used to continuously strengthen security, enabling customers to rapidly detect irregularities and minimize the impacts of problems. Furthermore, we believe it makes it possible to provide robust security that contains security incidents by rapidly responding to them and minimizes service down time.
Click here to move to the top of this page.
The Cyber-Security Center, aggregating the Toshiba Group's security functions

The Cyber-Security Center, established as an organization under the direct control of the Chief Information Security Officer (CISO), is a groundbreaking organization that combines both the functions of the Computer Security Incident Response Team (CSIRT), which responds to information security risks in the Toshiba Group, and of the Product Security Incident Response Team (PSIRT), which performs risk management for Toshiba products and services and the components that make them up. It brings together Toshiba's expertise and human resources to centrally manage security technologies and information about unknown threats and security incidents. It provides powerful support for industrial IoT security, with a broad-ranging perspective that covers both information systems and control systems.
The Cyber-Security Center also serves as a contact point for security-related organizations and security vendors, both inside Japan and abroad. In addition to serving as a rapid mediator between the split-off businesses that are Toshiba's implementing bodies, it also coordinates with Toshiba's Corporate Research & Development Center and Toshiba Digital Solutions Corporation to provide support for the latest security technologies and human resource development for those responsible for IoT security. It also plays a central role in governance, contributing to rapid decision-making by the CISO regarding major security incidents with the potential to affect business operation and rapid response within the Group.
Click here to move to the top of this page.
Internal evaluation of optimized security models corresponding to the evolution of digital transformation
Toshiba Digital Solutions is also establishing new security technologies. First, we have defined security measure levels for IoT systems applied to digital transformation, and formulated a "Security Reference Architecture" that corresponds with each level (Fig. 2).
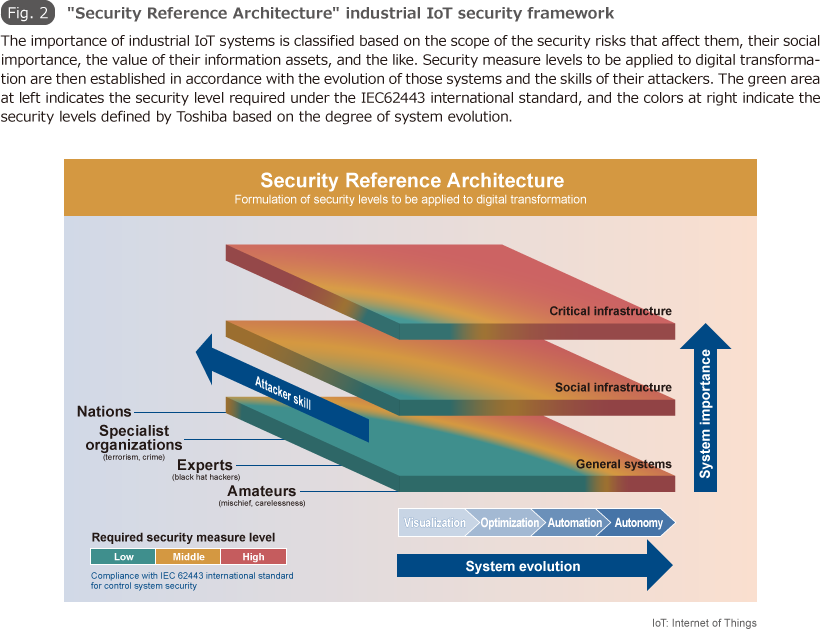
In addition to the importance of systems, such as whether systems are general systems or critical systems, stipulated in the IEC62443 international standard, our concept was to also formulate levels that correspond to the evolutions of IoT systems, such as "visualization -> optimization -> automation -> autonomy," producing designs which balance optimal security and cost.
Furthermore, we introduced the concept of "defense in depth" as a means of implementing measures. We created a “Dual Axis” security wall of defense in depth that combines the layers that make up product systems (depth), such as applications, middleware, OS, firmware, and hardware, with the layers that make up IoT system areas (width), such as external boundaries between systems and the outside world, internal boundaries between information systems and control systems, and internal nodes, such as control devices and equipment. By overlapping multiple layers of security with differing perspectives, we seek to make it possible to detect attacks during their initial stages and minimize the damage these attacks produce by slowing the attacks and detecting cyber-attacks before they cause damage.
We compare this defense in depth against the Security Reference Architecture to promote the creation of security models that are sufficient and effective for customer systems. We are now performing verification of multiple models, and in the future, we plan to define recommended models based on the characteristics of customer systems. We will also be performing internal verification of advanced technologies such as security gateways which physically cut off outside transmissions (attacks, etc.) while still being able to transmit data from within control networks, innovative devices that improve overall system security while retaining legacy endpoints, and using AI technology to detect threats.
We will protect customer business continuity and the safety and security of society from the cyber-attacks that threaten social infrastructure. We believe that is Toshiba's mission, which can only be achieved using the advanced and diverse technologies and expertise we have accrued. Starting with organizational reforms and the establishment of security concepts, Toshiba will continue to implement measures to constantly evolve the industrial IoT security that supports the era of IoT and the digital transformation it entails.
* The corporate names, organization names, job titles and other names and titles appearing in this article are those as of April 2018.